Protection for mobile devices and tablets
Dr.Web Mobile Security Suite — antivirus security for Android devices and tablets, as well as SmartTVs powered by Android TV

Unique technologies
Detects and neutralizes even brand-new threats targeting Android

Protects against phishing
Prevents users from visiting dangerous sites and blocks phishing attacks

Maintains privacy
Protects personal data and personal space when mobile devices are in use
Dr.Web Mobile Security Suite — an effective antivirus protection solution for mobile devices and tablets

Features (for Android)
-
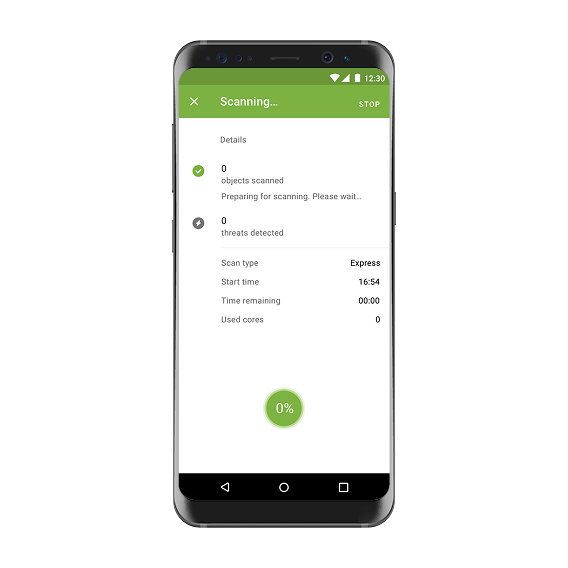
Multi-threaded scanning, with tasks distributed between CPU cores
-
Scans files received via a GPRS/Infrared/Bluetooth/Wi-Fi/USB connection or while synchronising with a computer
-
Full and custom scanning modes
-
The option to enable/disable resident protection for memory cards
-
Automated self-recovery
-
On-demand scanning of a device’s entire file system or separate files and folders
-
Scans APK, ZIP, SIS, CAB, RAR, and JAR archives
-
Blocks applications that are not on the administrator allowed list
-
Customizable rules for each application
-
Instant control over outgoing or incoming traffic for each application
-
Ability to restrict mobile data traffic
-
Ability to set roaming restrictions for specific applications
-
Ability to block access to non-recommended sites
-
Protects against unauthorized access via wireless networks
-
Neutralizes encryption ransomware
-
Vulnerability scanner
-
Blacklists and whitelists for filtering incoming calls and SMS messages
-
Support for multiple trusted SIM cards
-
Infected file deletion
-
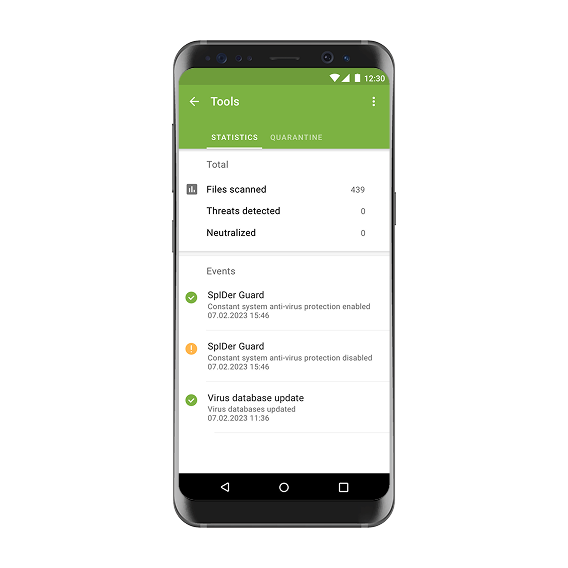
Quarantine for suspicious files
-
Option to restore files from the quarantine
-
Internet-based updates are downloaded:
• over HTTP using the GPRS module;
• via an Infrared/Bluetooth/Wi-Fi/USB connection;
• while synchronising with an Internet-connected PC via ActiveSync -
Detailed system scanning reports
-
Lock screen displaying information about detected threats and links to the threat list
-
Notifications about any activity detected that is typical of malware
-
The Anti-theft component to manage a lost or stolen device remotely
-
Mobile device GPS coordinates deliverable via SMS
Grow your cybersecurity confidence with Dr.Web Mobile Security Suite